Malware analysis Malicious activity
5
$ 38.00
In stock
(260)
Product Description
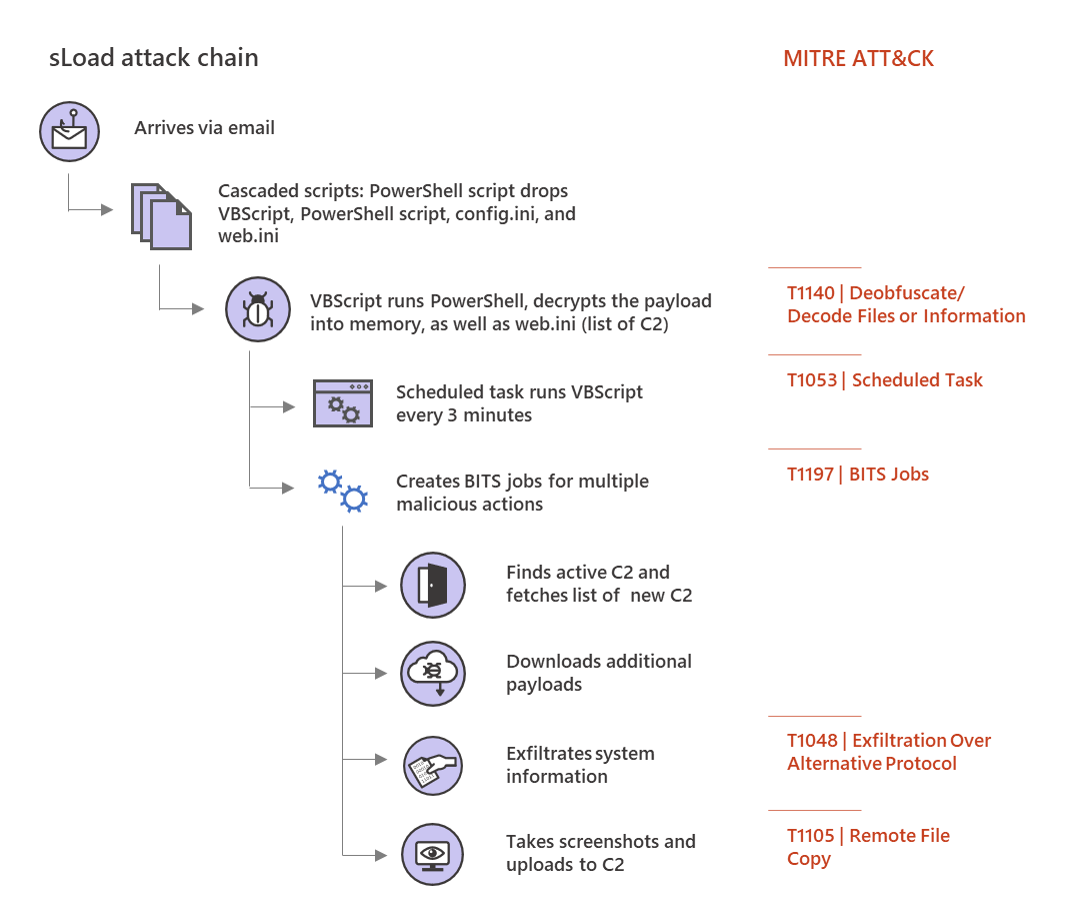
Multi-stage downloader Trojan sLoad abuses BITS almost exclusively for malicious activities

Malware Detection flowchart [64]
7 Best Malware Detection & Analysis Tools for Networks in 2023

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
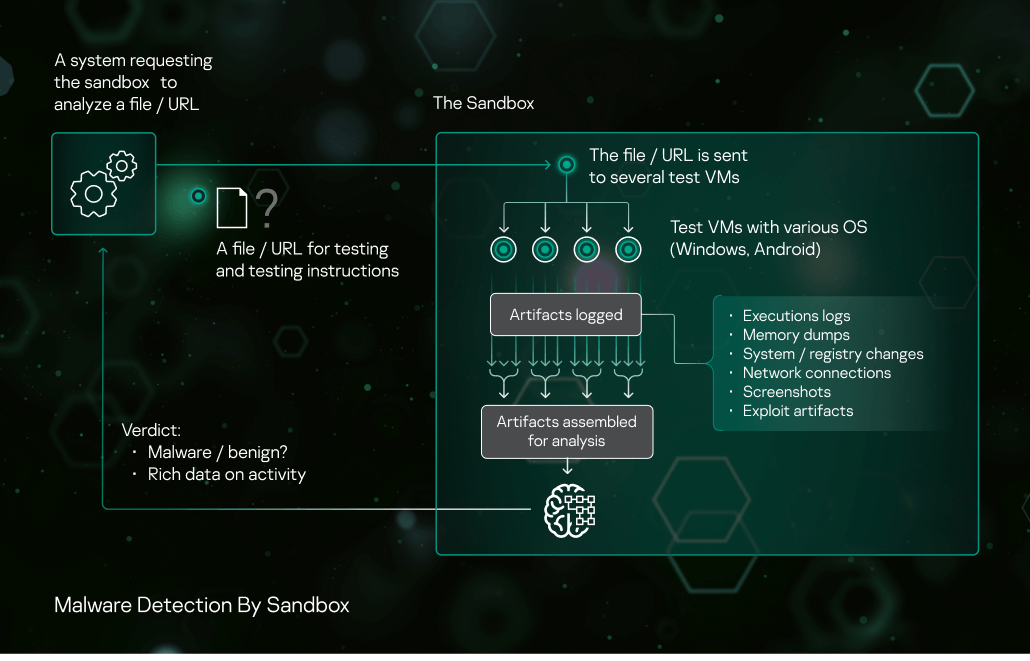
Sandbox Kaspersky
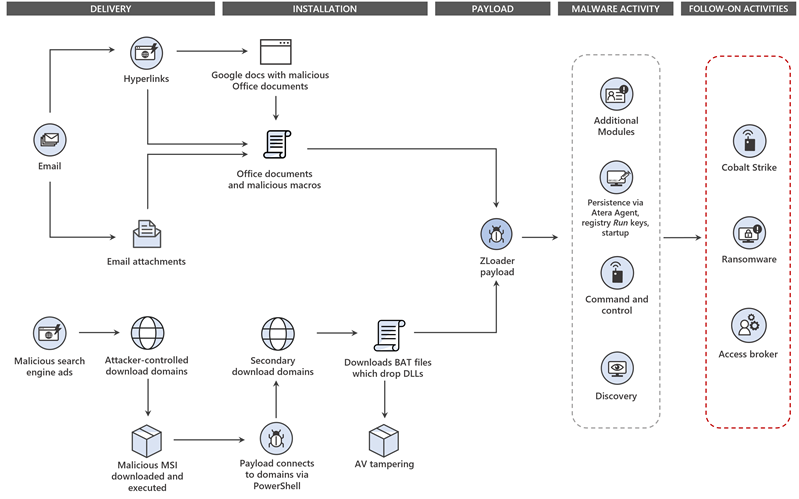
Dismantling ZLoader: How malicious ads led to disabled security tools and ransomware
Detect GraphSteel and GrimPlant Malware Delivered by UAC-0056 Group: CERT-UA Warns of Phishing Attacks Related to COVID-19 - SOC Prime

What is Malware Analysis
11 Best Malware Analysis Tools and Their Features
Applied Sciences, Free Full-Text

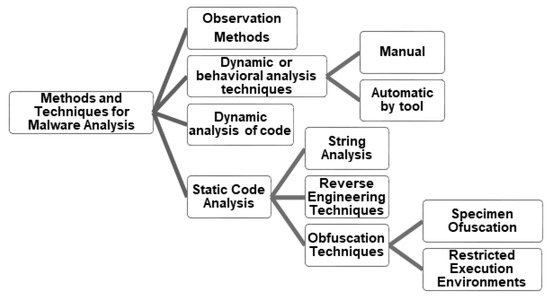
Dynamic malware analysis flowchart

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis Benefits Incident Response

7 open-source malware analysis tools you should try out - Help Net Security
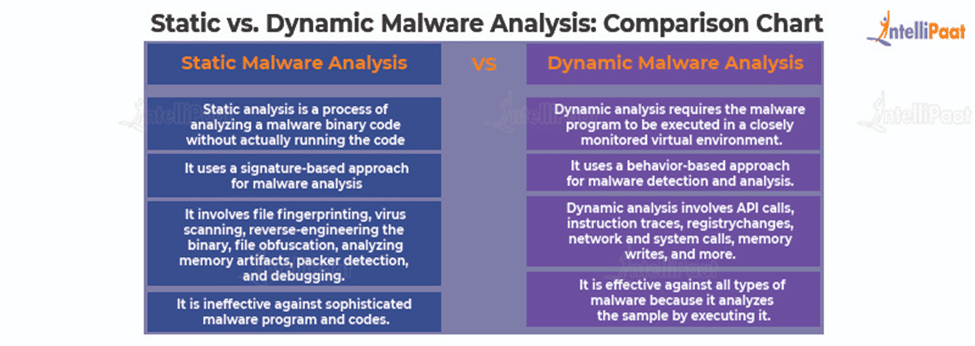
What is Malware Analysis?: Types and Stages Explained








